The Best Traffic Bot and Website Automation Software




Earn money by clicking ads
on your website or beat
your competitors by
clicking their AD
automatically.
Join popular freelancing
platforms like Fiverr, Seo
Clerks and start selling
website traffic there and
make some money!
They played it through cheap speakers. The chord held, imperfect but whole. Jamal felt his chest loosen in a way that had nothing to do with sound engineering. Mira laughed, shaking her head at the romanticism of it all, then turned solemn. "It’s fixed," she said, and both of them understood the different senses of the word: repaired, restored, and somehow set right.
She treated it like a puzzle. They scavenged the donated servers for old caches, checked forgotten torrent seeds, and wrote scripts to reconstruct corrupted MP3 frames from partial headers. Each recovered byte was a small victory — a grain of melody reassembled into rhythm, a breath here, a reverb tail there. On the third night, when the campus slept and rain ticked on the windows, a file they’d named freedom_rebuild_v7.mp3 began to make sense. It had gaps, but the crescendo at the end — that last line Jamal had whispered to himself for years — sat there, raw and honest.
Word spread quietly. Friends asked for copies. Jamal refused to post it online; the dark corners of the internet had been part of the song’s disappearance, and he didn’t want to drag it back there. Instead, he encoded a handful of burned CDs with hand-drawn covers and slipped them to people at shows, in
Back when he was sixteen, a broken hard drive and a lost backup erased his whole collection. For years he pieced tracks back together from memory, stray MP3s, and an old CD drive that spat out scratches and static. The single track he never could reclaim was the version of “Freedom” that ended the album — a fragile, late-night ballad Akon had slipped into the final minutes. Every attempt to find a clean copy ended in links that promised "free download" but delivered dead files, crude rips, or worse: truncated songs missing that last, aching line.
Mira smiled and asked questions that went beyond the usual: Had he tried metadata cross-matching? Any ID3 tags left from earlier versions? He confessed that he once downloaded an MP3 from a sketchy tracker marked "Akon_FREEDOM_mp3_free_download_FIXED.zip" and opened it without thinking. The file vanished after an antivirus sweep, and so did the trail.
Jamal had chased music rabbit holes since middle school. He built playlists like other kids collected stamps: neat folders, cover art he’d made in a tired midnight frenzy, and a folder named Freedom — Akon, the album that arrived in his life like summer rain after a drought. It was the one record that had taught him how to write hooks and ride a beat.
On a damp Thursday in April, the campus library announced it would donate outdated servers to a student hacking club. Jamal volunteered to haul them. In a basement lit by blinking LEDs, he met Mira, a systems grad with an old-soul laugh and a talent for data forensics. Over pizza and warm coffee, he told her about the missing song — the way the last chord felt like being told a secret.
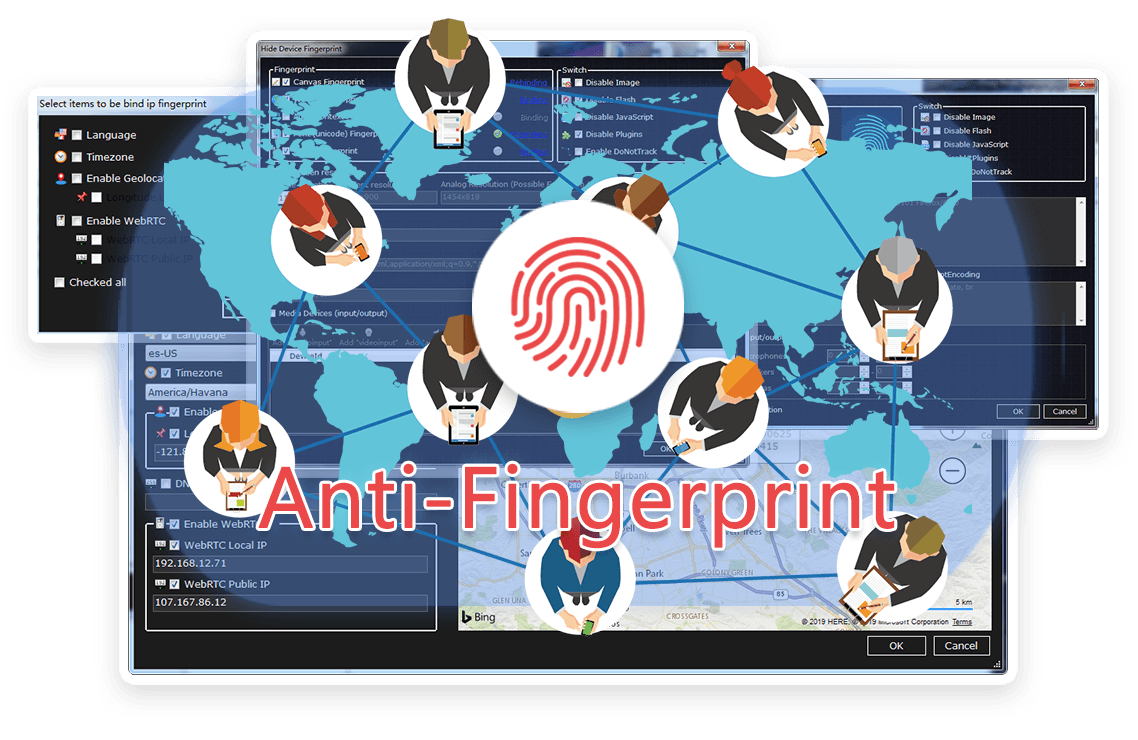
TrafficBotPro is a software web automation software that allows you to hide and control your digital
fingerprint by spoofing all parameters that websites can see. By masking these settings, you can bypass
anti-fraud systems by impersonating your real internet identity.
It helps you create a large number of profiles, each with its own digital fingerprint. These profiles do not
overlap with each other, so the website cannot ban your account. This is useful for performing various tasks
on the Internet.
Our software approaches browser fingerprinting in a completely indigenous way. Instead of trying to prevent websites from reading your computer’s fingerprint, our software allows reading it but replaces your original fingerprint with a different one. When you use a proxy IP, our software is fully different to other software that only add a proxy to your browser to work, our software will set the timezone, language, DNS and location etc... is matched to your proxy IP, that will make you looks like a real people from the proxy IP. Our software can also generate different device fingerprint and bind different fingerprint with your accounts. Once the account is bind with proxy IP, device fingerprint and other settings, the account will use these settings all the time with all operation. That is why you can use our software to mange and operate many accounts with different proxy safely.




They played it through cheap speakers. The chord held, imperfect but whole. Jamal felt his chest loosen in a way that had nothing to do with sound engineering. Mira laughed, shaking her head at the romanticism of it all, then turned solemn. "It’s fixed," she said, and both of them understood the different senses of the word: repaired, restored, and somehow set right.
She treated it like a puzzle. They scavenged the donated servers for old caches, checked forgotten torrent seeds, and wrote scripts to reconstruct corrupted MP3 frames from partial headers. Each recovered byte was a small victory — a grain of melody reassembled into rhythm, a breath here, a reverb tail there. On the third night, when the campus slept and rain ticked on the windows, a file they’d named freedom_rebuild_v7.mp3 began to make sense. It had gaps, but the crescendo at the end — that last line Jamal had whispered to himself for years — sat there, raw and honest. akon freedom mp3 album free download fixed
Word spread quietly. Friends asked for copies. Jamal refused to post it online; the dark corners of the internet had been part of the song’s disappearance, and he didn’t want to drag it back there. Instead, he encoded a handful of burned CDs with hand-drawn covers and slipped them to people at shows, in They played it through cheap speakers
Back when he was sixteen, a broken hard drive and a lost backup erased his whole collection. For years he pieced tracks back together from memory, stray MP3s, and an old CD drive that spat out scratches and static. The single track he never could reclaim was the version of “Freedom” that ended the album — a fragile, late-night ballad Akon had slipped into the final minutes. Every attempt to find a clean copy ended in links that promised "free download" but delivered dead files, crude rips, or worse: truncated songs missing that last, aching line. Mira laughed, shaking her head at the romanticism
Mira smiled and asked questions that went beyond the usual: Had he tried metadata cross-matching? Any ID3 tags left from earlier versions? He confessed that he once downloaded an MP3 from a sketchy tracker marked "Akon_FREEDOM_mp3_free_download_FIXED.zip" and opened it without thinking. The file vanished after an antivirus sweep, and so did the trail.
Jamal had chased music rabbit holes since middle school. He built playlists like other kids collected stamps: neat folders, cover art he’d made in a tired midnight frenzy, and a folder named Freedom — Akon, the album that arrived in his life like summer rain after a drought. It was the one record that had taught him how to write hooks and ride a beat.
On a damp Thursday in April, the campus library announced it would donate outdated servers to a student hacking club. Jamal volunteered to haul them. In a basement lit by blinking LEDs, he met Mira, a systems grad with an old-soul laugh and a talent for data forensics. Over pizza and warm coffee, he told her about the missing song — the way the last chord felt like being told a secret.
Browse the latest blog posts for in-depth insights into anti-detection and online privacy. Stay up-to-date!


Submit your need here, we will check and give you reply asap.
